Is Metaverse the Next Big Disruption, and How Can IT Leadership Prepare to Benefit from It?

The metaverse is the next big thing in the tech world. Like AI, the metaverse promises big-scale disruption. But how can enterprises leverage the coming disruption to their advantage? The metaverse is a convergence of the physical and the virtual worlds. Users can recreate the physical experience in the digital sphere in an immersive mode. […]
The New CIO: From a Tech Expert to a Business Leader and Strategist
It is no longer enough for the chief information officer (CIO) to be competent in technology. They have new responsibilities that go much beyond technology. And with new responsibilities come new challenges. Today, a successful CIO is a business strategist with deep technical expertise. The Increasing Business Responsibilities of the CIO Around two decades back, […]
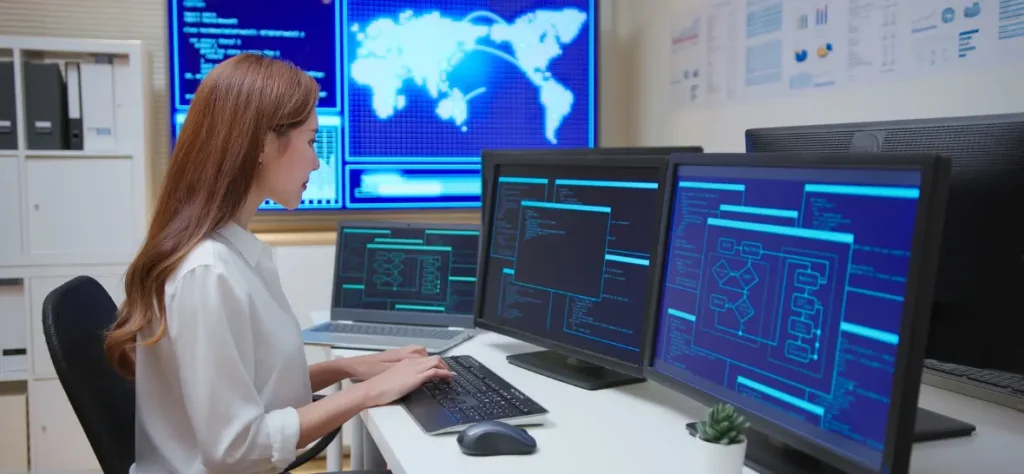
Best Practices to Detect and Remediate Threats and Secure Endpoints
In today’s work from anywhere, a cloud-based environment, users and devices always operate in a hostile environment. Conventional perimeter-focused security approaches no longer work. Today, network users and devices connect to the network from far-off places. Each point of connection represents an endpoint. A majority of such endpoints are beyond the conventional network perimeter. And […]
How Does Customer Data Platforms (CDP) Add Value to Enterprises

Big data promises huge opportunities. But most enterprises underperform with Big Data. They incur huge overheads on data management without proportional returns. Many enterprises feel left out, being unable to make sense of their data. A majority of enterprises still struggle to capture relevant data. They collect huge swathes of irrelevant data and struggle with […]
The Myths and Misconceptions about Low Code Platforms
Low-code platforms enable fast and easy development of enterprise applications. The users do not need coding or technical expertise. Business users can get things done without waiting for coding experts. But does this theory hold good in actual practice? Why is the adoption of low-code platforms at the enterprise level still limited? Many myths and […]
The Rise of Ransomware-as-a-Service: How to Protect Your Organisation

Ransomware attacks continue to rise. Today, about 43000 ransomware attacks take place worldwide, every single day, on average. A 2024 survey reveals ransomware attacks hit 75% of the surveyed enterprises, and the majority of the enterprises faced multiple attacks in a year. The common modus operandi is for attackers to infiltrate networks using phishing or […]
How Will Autonomous AI Systems Change the World?
Will autonomous AI disrupt businesses and lives? Or are the predictions of far-reaching disruption hype? Until now, most businesses have used AI-powered systems to make existing processes better and faster. AI resembles a knowledgeable employee who does not speak until spoken to and someone who does his brief well but does not think out of […]
Is Your Encrypted File Storage Actually Safe?

Conventional, perimeter-based security has become obsolete in today’s Internet era. Enterprise data lies scattered across the cloud. And most enterprise data is outside the company’s perimeter. With data moving around in cyberspace, encryption has become a basic requirement for data security. But is encryption the holy grail of data security? Is it as impenetrable as […]
Will AI Take Over Software Testing Jobs?
Application integrity and user-friendliness have become non-negotiable in today’s competitive marketplace. Six out of ten users abandon online purchases if they have a poor experience. Comprehensive testing is indispensable to deliver impeccable and resilient software capable of delighting customers and withstanding all environmental shocks. But conventional, manual testing cannot do a complete job to test […]
Best Practices to Optimise Data Storage Costs

Data is today a top business commodity. But system and user-generated data add up. For many enterprises, data storage costs dent the bottom line. Without optimising data storage costs, the benefits derived from the data may not exceed the data costs. Here are the best practices to optimise data storage costs. 1. Save Only Essential […]
How CXOs Can Use GPT-4 and Streaming Data to Generate Real-Time Insights
GenAI is now a household phenomenon. Large Language Models (LLM) models interpret complex datasets to discover patterns. But genAI does not find use in business applications that depend on real-time proprietary data feeds. Integrating genAI capabilities with live business data is still a challenge. The Importance of Streaming Data Today, the bulk of relevant enterprise […]
How to Reduce the Attack Surface and Protect Today’s Spread Out Networks

If you are still running conventional perimeter-based security, you are living dangerously. Threat actors could breach your network easily from anywhere and destroy your business. The conventional “castle-and-moat” perimeter-based security approach worked well when the attack surface was small and limited. The attack surface is all potential entry points that attackers can use to compromise […]